WikiLeaks Releases Documents from the ELSA Project of CIA
ELSA Project of CIA
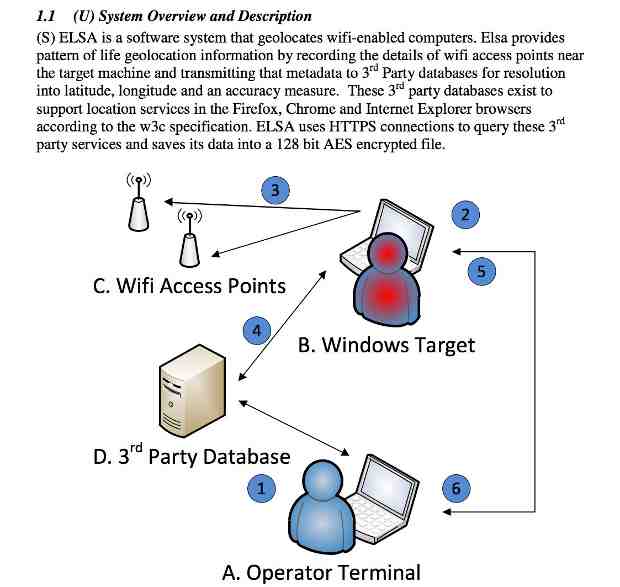
WikiLeaks published Wednesday documents from the ELSA project of the U.S. Central Intelligence Agency (CIA). ELSA is a geo-location malware for WiFi-enabled devices like laptops running the Micorosoft Windows operating system.
Once persistently installed on a target machine using separate CIA exploits, the malware scans visible WiFi access points and records the ESS identifier, MAC address and signal strength at regular intervals.
According to WikiLeaks, in order to perform the data collection the target machine does not have to be online or connected to an access point; it only needs to be running with an enabled WiFi device.
[ WikiLeaks Asks: Do You Want to See Secret Tax Returns of Donald Trump? ]
If it is connected to the internet, the malware automatically tries to use public geo-location databases from Google or Microsoft to resolve the position of the device and stores the longitude and latitude data along with the timestamp.
The collected access point/geo-location information is stored in encrypted form on the device for later exfiltration. The malware itself does not beacon this data to a CIA back-end; instead the operator must actively retrieve the log file from the device – again using separate CIA exploits and backdoors.
[ Democracy 2.0: Aadhaar Data May be Used for Voting Frauds in India ]
The ELSA project, according to WikiLeaks, allows the customization of the implant to match the target environment and operational objectives like sampling interval, maximum size of the logfile and invocation / persistence method.
Additional back-end software (again using public geo-location databases from Google and Microsoft) converts unprocessed access point information from exfiltrated logfiles to geo-location data to create a tracking profile of the target device.
Photo courtesy: WikiLeaks











